CS 257 - Fall 2020.
[Home]
Welcome to CS 257!
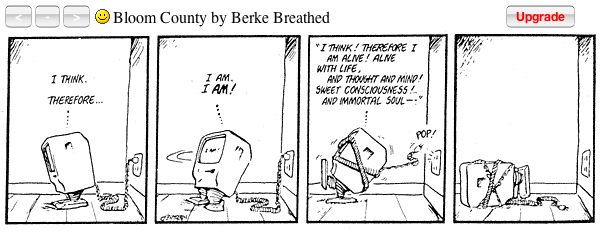
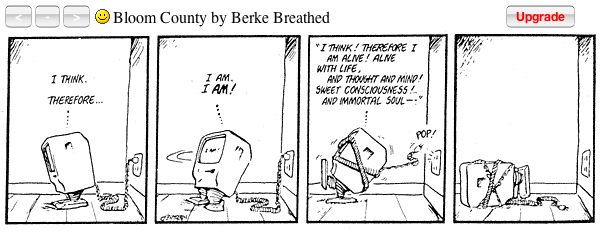
Thought for the day
Schneier's Law:
Any person can invent a security system so clever that he or she
can't imagine a way of breaking it.
Lecture 2: Crypto. 9/7
Administrivia
Office hours (via zoom. Meeting ID 459 434 2854): Wednesday 4 to 6 pm,
and by appointment.
Complete
this online Student Information form. So far, everyone is in EDT time zone.
Get a course account for CPSC 257 on the Zoo. When you register for
this class, your course account should be created within one hour or
so of signing up.
Confirm your piazza account.
Start the homework assignment:
[Assignments]. Demonstrate openssl
Python code to help get started: hw1.py.
base64
echo hello | openssl base64
aGVsbG8K
h is ascii 0150 = 01101000
011010 == 26 == a in base64
Google Python Class Most of you seem to know python.
Lecture
Chapter 2: Crypto Overview
slides: chapter 2 (slide 28)
Classic crypto methods
-
Spartan Scytale Transposition cipher
- Substitution Cypher, e.g., Poe's The Gold Bug
- Double transposition
- One-time pad (XOR ⊕ magic!)
- Codebook
- Election of 1876.
- Not decided by the Supreme Court – commission was 8 republicans
and 7 democrats. Guess what?
- Tilden won 184 votes (and popular vote!)
- Hayes won 165. 20 votes were in dispute.
- States included Florida, Louisiana, South Carolina, and one disputed elector in Oregon.
- Compromise: Democrats awarded 20 votes to Hayes in return for
withdrawal of federal troops from the South to end Reconstruction.
- Tilden was trying to bribe officials.
He had accused Hayes of bribery.
- Battle of Midway
- Allies claimed water shortage at Midway (broken desalination plant)
- Saved 100,000+ lives and 1+ years
- Post-WWII History
- Before Shannon, crypto had been a black art
- DES marked an inflection point – cryptography came out of the shadows.
- Claude Shannon
- Diffusion does not erase single character frequency counts, but removes bi-grams.
- Election of 1876 used both confusion (code book) and diffusion (permutation), albeit both were pretty lame.
- Taxonomy of Cryptography
- Key distribution problem with symmetric keys
- Digital signatures – use private key to encrypt authenticated documents
- Taxonomy of Cryptanalysis
- Forward search.
- Example- get ciphertext that could be “yes” or “no”
Use public key to encrypt “yes” and “no” and compare. Either a match or something else.
- Defense: pad the message with 64 bits. Then have 2^64 versions of yes
- Can also forward email message: “Please forward the attached to Bob”
Chapter 3: Symmetric Key
slides: chapter 3 (actually 2-6)
slides: chapter 3 4 up
Symmetric Key Crypto
- Stream ciphers are more practical version of one time pad.
- Stretch out stream to length of message and xor.
Stream Ciphers
Stream Ciphers
- A5/1 – implemented in hardware – at that time, processor speed was slow.
- RC4 – possible to implement in software
- Used a lot: WEP (Wired Equivalent Privacy IEEE 802.11 wireless networks) often the first choice presented to users by router configuration tools.
- 2003 superceded by WPA – Wi-Fi Protected Access., 802.11i (WPA2) standard – deprecated WEP-40 and WEP-104
- WEP-40 has 40 bit key and 24 bit initialization vector (IV) == 10 hexadecimal digits
- 40 bit key can be 5 ASCII characters of 8 bits each.
- WEP-104 is 26 hex characters, with 26 4 bit characters plus 24 bit IV
, TLS
A5/1 - Shift Registers
- Total of 64 bits
- Implemented in hardware
- A5/1 wiki - design shrouded in secrecy. We do not know why it was designed this way.
- If bit is in the majority, then that register steps.
- 2 or 3 registers always step
- Generates a single bit for xor
Shift Register Crypto: Phone / voice is roughly 64K bits per second
RC4
-
256 Byte values
- Table is a permutation of those values
- Invented by Ron Rivest in 1987
-
RC4 stands for Rivest Cipher 4, but is trademarked by Rivest’s company, RSA.
- Also, Ron’s Code. (RC2, RC5, RC6)
- Was initially a trade secret, but description was posted in 1994, which was then broken by Bob Jenkins within days. While never acknowledged, the leaked code was found to match the proprietary software.
- How does Kerkhoff’s principal apply here?
- The array keeps changing, makes it harder to break.
Stream Ciphers
- Rivest makes ‘em and Shamir breaks ‘em.
- Stream ciphers, like the old man in Monty Python’s Holy Grail, are not dead yet.
- They can fit on small devices, like IoT.
Block Ciphers
Feistel Cipher
- Feistel worked at IBM.
- Born in Berlin. Came to US in 1934. WWII under house arrest
until 1944 when became a US citizen, got a security clearance, and
worked for the air force on IFF (Identification of Friend or Foe). BS
from MIT and MS from Harvard in Physics. Developed Lucifer which
became DES
- For decryption: if F(R,K) == 0, then P == C
Data Encryption Standard (DES)
- NBS == National Bureau of Standards
- Which became NIST = National Institute of Standards and Technology
- Issue RFP, and got only a handful of responses. Indicating that there was not much going on the cryptography world.
- After NSA involvement, people were suspicious – suspected an NSA backdoor.
- Result – much more interest in cryptography.
- 256 possible codebooks
- The S-boxes are lookup tables.
- It is a Feistel Cipher
- 8 S boxes convert 48 bits to 32 bits
DES S-box
- S box is just a look up table
- Each row is a permutation
- 6 bits in and 4 bits out
- 48 bits becomes 32 bits
Security of DES
- Linear functions are easy to solve
- The S boxes are not linear – make the algorithm stronger
Block Cipher Notation
- This is a code book
- Use a different key, get a different code book
Triple DES: Not 3 * keys – just 2 keys
Advanced Encryption Standard (AES)
- AES Process which, by contrast to A5/1, was transparent.
- Conference among contestants
- Each wants to shoot holes in other ciphers
- Lots of criticism
- Feistel cipher is easy to decrypt. Here you need an invertible function
AES Summary
- DES has 64 bit block
- 56 bit key length
- 16 rounds
- But AES is more complicated
Time for TEA
- You will implement this in homework.
- Opposite of AES, which has strong round function and few rounds
- Delta is magic number – bits in the decimal expansion of sqrt(5)
- 32 rounds here are like 64 rounds of DES
- Not a Feistel cipher – does not use XOR
Block Cipher Modes
Multiple Blocks
- 56 bit key per block
- Bad idea to encrypt independently
- Partial blocks addressed with padding.
ECB mode: Never use ECB Mode!
CBC mode
- Most popular
- XOR magic!
- ADDITIVE analogy
- A single data transmission error can mess up 2 blocks – but not more.
Counter Mode (CTR): Note: not a typo – E() for decryption!
Integrity
Confidentiality: no unauthorized reading
Integrity – not changing data
MAC
- Multiple meanings of MAC
- MIC – message integrity code
- We said that errors do not propagate in CBC
That is in decryption, but not encryption.
Uses for Symmetric Crypto
- US Navy – John Walker would distribute keys-
- Side business selling keys to soviets
- Weak link in the system
[Home]